Key concepts of access control
Before you begin using and configuring access control, review and evaluate these key concepts that help you plan your access control and division setup:
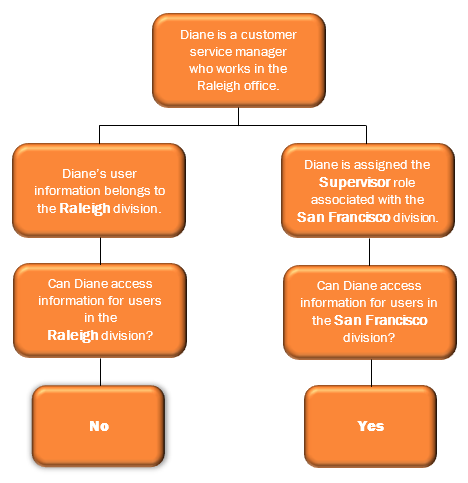
A user can be a configuration object within a division. However, an administrator can also grant a user permission to access a division. Moving a user into a division does not give that user access to the data within the division. The user’s data, such as profile information, is part of the division, and users who have the appropriate division permission assigned can access that data.
For more information, see Distinguish users as objects vs. users with access in Access control overview.
Example
Configuration objects
Configuration objects are specific resources within the organization. These resources include:
- Call routing objects
- Coaching appointments
- Contact lists
- Data tables
- Do not contact lists
- Emergencies
- Extensions
- Flows
- Flow milestones
- Flow outcomes
- Learning modules
- Management units
- Message routing objects
- Outbound campaigns
- Queues
- Schedules
- Schedule groups
- Scripts
- Users
While these objects are not the only configurable objects that exist in Genesys Cloud, they are the only ones protected by access control. Administrators can group and associate specific Genesys Cloud configuration objects within a division and then, using access control, selectively grant access to the objects in that division.
Transactional objects
Transactional objects are objects that interact with or travel through the system.
Transactional objects include:
- Voice, callback, chat, email, and message conversations
- Recordings
- Presence history
- Audit data
While these objects are not the only transactional objects that exist in Genesys Cloud, they are the only ones protected by access control.
For more information, see Access control configuration objects and Access control transactional objects.
Evaluate all client credential grants and determine what divisions to associate with the grant’s roles. By default, the system scopes all client credential grant roles to the Home division. To ensure that the application and the systems using a client credentials grant can access the appropriate data, update the assigned roles with appropriate divisions. If a third party supplies the client credential grant, confirm the use of the grant and then update the divisions for the roles accordingly.
For more information, see Create an OAuth client.
By default, Authorized Users have the All Divisions and All Future Divisions tags associated with their roles. For more information, see Access control for authorized users and groups in Divisions overview.
Only the users that have Queue > View permissions on roles with the specific division for the queue can receive reports. You may need to adjust users divisions associated with their roles to allow them to continue receiving reports.
Before you begin configuring access control, review your organizational needs and determine how you want to implement access control. Consider the following:
Divisions
- How do you want to organize your divisions? For example, by region, office location, or business unit.
- Do you want to grant users the access to manage objects in all divisions, or only in specific divisions? If so, identify those users and the divisions in which you want them to administer objects.
Configurable and transactional objects
- Which configuration objects (users, queues, flows, management units, campaigns, contact lists, Do Not Contact lists) do you want to move into each division?
- Are there configuration objects that do not fit into a specific division? What do you want to do with those objects and who do you want to administer them?
- Do you want to limit access to transactional objects (for example, interactions)?
Decide if you want to first configure and test a single division, and then configure and test more divisions. You may also configure divisions during off-hours to ensure it has no impact on ongoing activities. Best practice recommends that you:
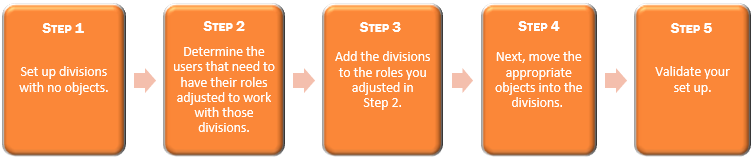
As you add divisions to roles for users, consider leaving the default Home division on the roles and then adding new divisions. This process avoids any initial loss of access to objects in the Home Division. After you complete and test your setup, remove the Home division from the roles.

