Gather network logs on the desktop app
Genesys Cloud Product Support uses console network logs, also called network logs, to troubleshoot and diagnose various problems. The network log helps diagnose WebRTC issues. In addition, it helps with call control issues.
When problems occur, console and network logs provide visibility into the actions and events on an agent’s computer. Troubleshooting issues without complete information can be difficult. However, when combined with Cloud-side logging, browser logs (console logs and network logs) provide Product Support with a full picture of the issue.
To get a network log with the Genesys Cloud desktop app, start by configuring Genesys Cloud to show the console.
- To display the console, use advanced preferences.
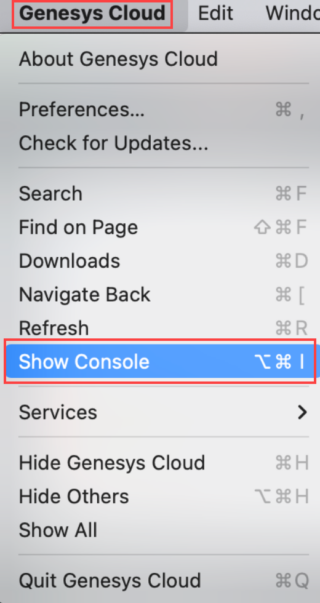
- Simultaneously press the Option key and click Genesys Cloud > Advanced Preferences…
- Select the Enable Developer Tools checkbox.
- Click Genesys Cloud a second time and click Show Console.
 The console appears.
The console appears.
- Click the Genesys Cloud icon and click Advanced Preferences.
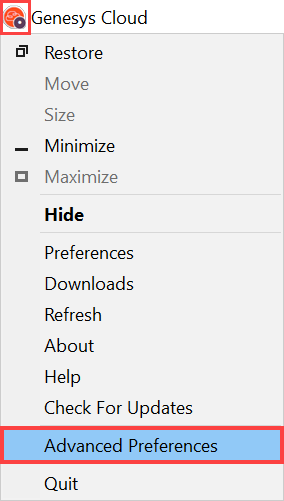
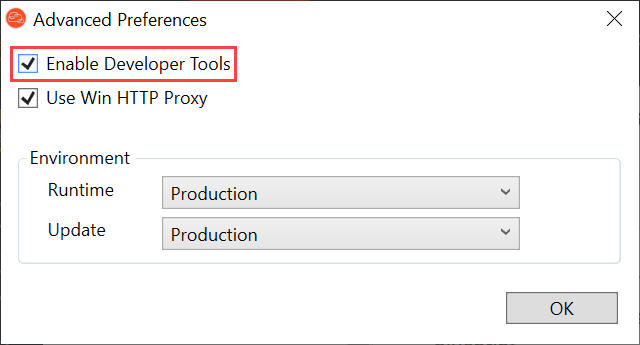
- Select the Enable Developer Tools checkbox and click OK.
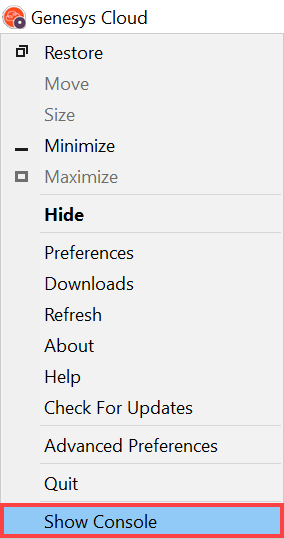
- Click the Genesys Cloud icon again and click Show Console.
 The console appears.
The console appears.
- Click the Network tab.
- Select the Preserve log checkbox.
- To the upper left of the console, click Clear network log .
- Leave the console open and reproduce the issue.
- After you reproduce the issue, right-click on any line, select Save all as HAR with content, and then save the file.Note: If you copy or move log files soon after saving, they can break. Ensure to wait for the data transfer to complete after saving the file and then, move the file to a different location or upload the file to the Support ticket.
- Upload this file to your Support ticket along with any other requested info. Use My Support to open and manage your support cases.Note: Ensure to redact or scrub user passwords from the HAR files that you upload, if relevant. If necessary, you can ensure that users change their passwords after the logs have been captured.

